Permanent access clearance with physical or digital access cards
The changing geopolitical situation places new demands on the security of ports and critical infrastructure.
Increased security through person-centricity and two-factor authentication before passage
The trend is moving towards cards and PIN codes as a minimum requirement for access to restricted port areas. When digital cards are used, a code is increasingly required in combination. The same development is taking place for visitors and short-term access, which previously relied on one-time or period-based codes. Today, ports increasingly combine LPR recognition, digital cards, and PIN codes for temporary access.
Solutions where tags and printed access permits remain in vehicles regardless of the driver are gradually being phased out as security plans are updated. Increased security requirements can quickly become resource-intensive if processes are not digitised and systems integrated.
Companies with security agreements can apply for cards
The Port Security Agreement regulates company-specific authorisations and responsibilities and provides access to the system’s self-service portal for card and visitor applications. The agreement regulates which areas the company can apply access to, required training for these areas, rights to issue temporary cards for projects, and pricing for new cards, replacement cards, and annual fees.
The solution gives the port control over visitors and access rights issued. It also makes it possible to require certain visitors to apply for permanent access cards, improving security, training compliance, and traceability while reducing administration.
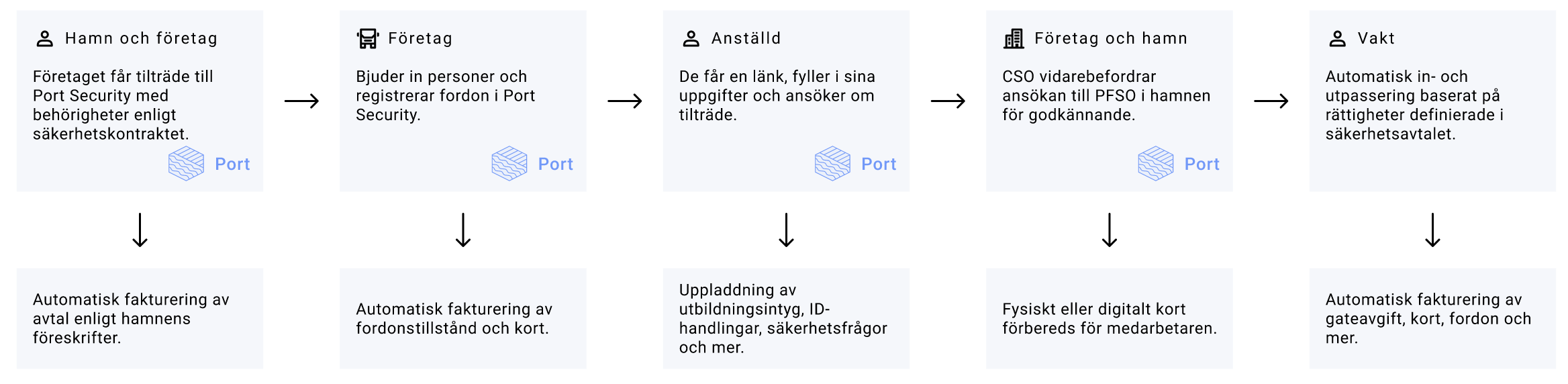
Image. Process for applying for permanent access
Applying for a card – digitally or physically
The company receives login credentials when the security agreement is signed, and the application process normally starts when an employee or contractor is invited to apply for access.
The company is responsible for managing applications for its personnel. The purpose is to reduce administration for the port while maintaining control over authorisations.
Applicants cannot apply for higher access rights than what the security agreement allows, creating the foundation for a digital approval process. During the process, all information required to produce a physical card or configure a digital card is registered. Photos, PIN codes, certificates, and required training are handled directly in the process before the application is submitted for approval by the company’s security officer and then forwarded to the port’s PFSO.
Integration to passage systems for manufacturing and activation
When the application is completed and approved, all required data is transferred automatically to the access control system where physical cards are produced and activated or digital cards configured.
Throughout the application process, the card moves through different statuses, and the system continuously notifies applicants and approvers if information is missing or actions are required. The process should not stop because information is missing or approvals are delayed.
The overall status and security overview are available through the security dashboard.
Active cards – follow-up, communication and invoicing
When the card becomes active, the system starts monitoring validity periods, training requirements, and access activity. Passage logs can be used for follow-up, traffic analysis, turnaround times, and historical documentation.
If important operational or security-related information needs to be communicated to users with specific access rights, the port can use the mass communication module to send targeted information directly to affected users or companies.
The same module can also be used to notify companies ahead of annual invoicing. This gives customers the opportunity to review and clean up unused cards before invoicing takes place, reducing unnecessary administration and follow-up work for both the port and its customers.
